Password Encryption – What It is and How it Works?

Password encryption is the process of converting plain text passwords into encoded and unreadable formats, with the aim of securing sensitive information such as user login credentials. The primary purpose of password encryption is to prevent unauthorized access to user accounts, which is essential for maintaining data privacy and security. Encryption is widely used in various digital platforms, including online banking, email services, and social media networks, among others.
In this article, we will discuss what password encryption is, how it works, and the different types of encryption techniques used to secure passwords.
What is Password Encryption?
Password encryption is a security measure used to protect sensitive data, specifically user credentials, by converting them into unreadable formats. The purpose of encryption is to prevent hackers and other unauthorized parties from gaining access to user accounts and other confidential data. When properly implemented, password encryption provides an effective layer of protection against malicious attackers.
We must initially become acquainted with the language to make sense of password encryption. Here is a brief overview of password encryption terminology to help you understand some terms that may be foreign to you.
Encryption Key: A string of bits used to encrypt and decrypt data.
Cryptography: Using algorithms, ciphers, and other techniques to protect data securely.
Plain Text/Clear Text: Data, such as passwords and usernames, that is readable in its original form.
Cipher Text: Encrypted data that is unreadable and unintelligible without a decryption key.
Hash Function: An algorithm used to convert plain text into encrypted ciphertext.
Salt: An additional layer of security is added when encrypting a password. It is generated randomly and stored in the user’s account.
Why You Should Encrypt Your Passwords?
Password Encryption is one of the most important steps to ensure your security online. With cybercrime becoming an increasingly costly and prevalent issue, it’s crucial for users to arm themselves with reliable protection. Encryption works by encoding digital data so that only those with a key can access it.
Not only does this prevent unauthorized individuals from being able to hijack your accounts, but it also guarantees that any person who could gain access, such as a hacker or government agency, won’t be able to actually read the data stored in them. In short, encrypting your passwords is necessary for protecting yourself from both malicious parties and increasingly intrusive surveillance efforts. Don’t risk your own personal security.
Password Encryption Work Process:
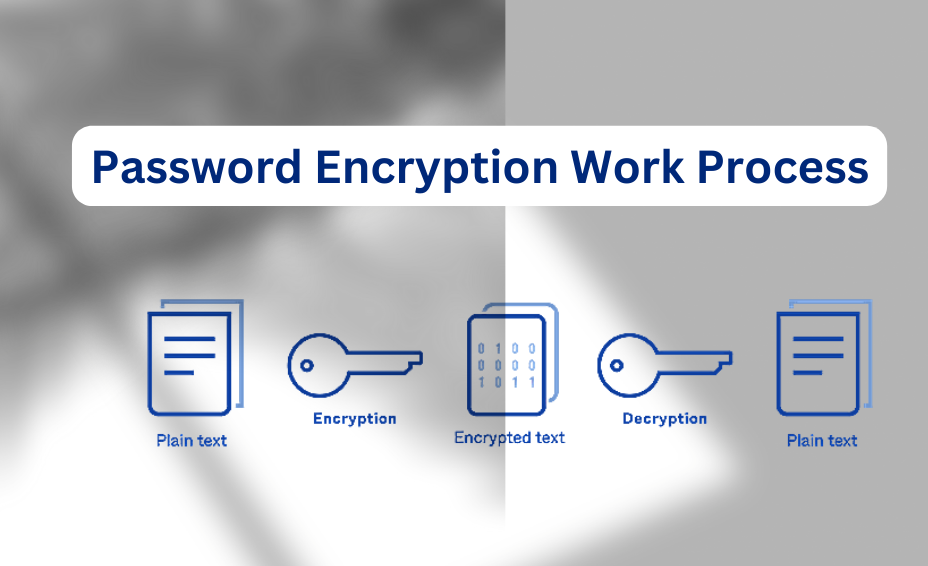
Password encryption typically works by using a cryptographic algorithm to convert plain text passwords into an encoded format. This scrambled format is called a “hash.” A hash is a unique string of characters that is generated through a complex mathematical algorithm that makes it almost impossible to revert to the original plaintext password.
The password they enter is encrypted, and the system compares the hashed value of the entered password with the stored hash value in the system’s database when a user logs in. If the two hashes match, the user is granted access to their account.
How Does Password Encryption Work?
The encryption of passwords follows a specific set of steps to ensure the highest level of security. The following are the typical steps involved in password encryption:
- A user inputs their password
The user types in their password in plain text form.
- Hashing the password
The plaintext password is then converted into an unreadable hash using a one-way hashing algorithm. The hash value is then stored in the database, replacing the original plaintext password.
- Verification of the entered password
When the user tries to log in, the entered password is hashed using the same algorithm used during registration. The resulting hash is then compared with the stored hash in the database. If the two hashes match, the user is granted access to their account.
Types of Password Encryption Techniques:
There are different types of encryption techniques used to secure passwords. The following are some of the most commonly used techniques:
SHA (Secure Hash Algorithm):
SHA is a widely used hashing algorithm that generates a 160-bit hash value. It is a one-way algorithm, meaning that it is virtually impossible to reverse the process and recover the original plaintext password. This technique is widely used in online banking and e-commerce platforms.
Bcrypt:
Bcrypt is a widely used password hashing algorithm that was developed in 1999. It is a key derivation function that uses a salted hash algorithm to secure passwords. Bcrypt uses a variable work factor, which makes it a computationally intensive technique that can effectively protect against brute-force attacks.
PBKDF2 (Password-Based Key Derivation Function 2):
PBKDF2 is a key derivation function that uses a salted hash algorithm to secure passwords. This technique is designed to be computationally intensive, making it challenging for attackers to perform brute-force attacks. PBKDF2 is used by various email services, including Gmail and Yahoo.
Scrypt:
Scrypt is a key derivation function that uses a memory-hard hash algorithm to secure passwords. It is designed to be computationally expensive, which makes it a more secure technique for password encryption. This technique is used by various online services, including Bitcoin wallets and file storage platforms.
Benefits of Password Encryption:

Password encryption provides a number of benefits, including:
- Encrypting passwords makes it virtually impossible for attackers to gain access to user accounts, even if the database storing the passwords is breached.
- It ensures that user data remains private, as the passwords are stored in an unreadable format.
- Encrypted passwords are more reliable, as they cannot be changed or manipulated by a third party.
- It is more difficult for attackers to crack, reducing the risk of unauthorized access to user accounts.
- Encrypted passwords make it easier for users to securely store and access their account information.
- Password encryption also provides an extra layer of security in remote working environments, where data is often stored and shared across different systems.
Conclusion
Password encryption is an essential security measure used to protect user login credentials and other sensitive information. Encryption involves converting plaintext passwords into unreadable hashes, making it challenging for attackers to access user accounts. There are different types of password encryption techniques, including SHA, Hope this brief article will be worth reading for you.